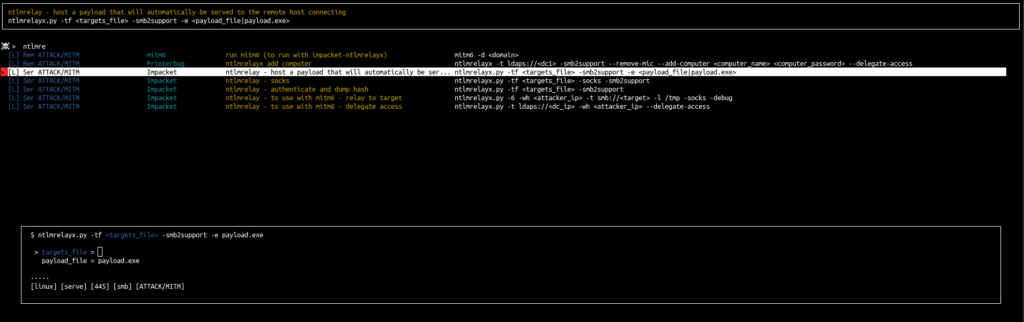
Arsenal is just a quick inventory, reminder and launcher for pentest commands.
This project written by pentesters for pentesters simplify the use of all the hard-to-remember commands.
In arsenal you can search for a command, select one and it’s prefilled directly in your terminal. This functionality is independent of the shell used. Indeed arsenal emulates real user input (with TTY arguments and IOCTL) so arsenal works with all shells and your commands will be in the history.
You have to enter arguments if needed, but arsenal supports global variables.
For example, during a pentest we can set the variable ip to prefill all commands using an ip with the right one.
To do that you just have to enter the following command in arsenal:
>set ip=10.10.10.10Authors:
- Guillaume Muh
- mayfly
This project is inspired by navi (https://github.com/denisidoro/navi) because the original version was in bash and too hard to understand to add features
Arsenal new features
- New colors
- Add tmux new pane support (with -t)
- Add default values in cheatsheets commands with
<argument|default_value> - Support description inside cheatsheets
- New categories and Tags
- New cheatsheets
- Add yml support (thx @0xswitch )
- Add fzf support with ctrl+t (thx @mgp25)
Install & Launch
- with
pip:
python3 -m pip install arsenal-cli- manually:
git clone https://github.com/Orange-Cyberdefense/arsenal.git
cd arsenal
python3 -m pip install -r requirements.txt
./runInside your .bashrc or .zshrc add the path to run to help you do that you could launch the addalias.sh script
./addalias.shLaunch in tmux mode
./run -t # if you launch arsenal in a tmux window with one pane, it will split the window and send the command to the otherpane without quitting arsenal
# if the window is already splited the command will be send to the other pane without quitting arsenal
./run -t -e # just like the -t mode but with direct execution in the other pane without quitting arsenalAdd external cheatsheets
You could add your own cheatsheets insode the my_cheats folder or in the ~/.cheats folder.
You could also add additional paths to the file <arsenal_home>/arsenal/modules/config.py, arsenal reads .md (MarkDown) and .rst (RestructuredText).
CHEATS_PATHS = [
join(BASEPATH, "cheats"), # DEFAULT
join(HOMEPATH, "docs/my_cheats")
]Cheatsheets examples are in <arsenal_home>/cheats: README.md and README.rst
Troubleshooting
If you got on error on color init try :
export TERM='xterm-256color'Mindmap
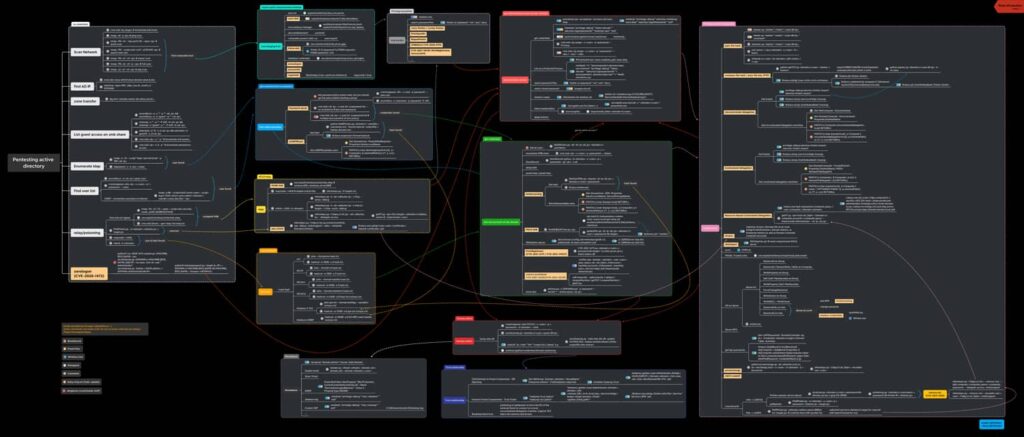
Active directory mindmap

AD mindmap black version
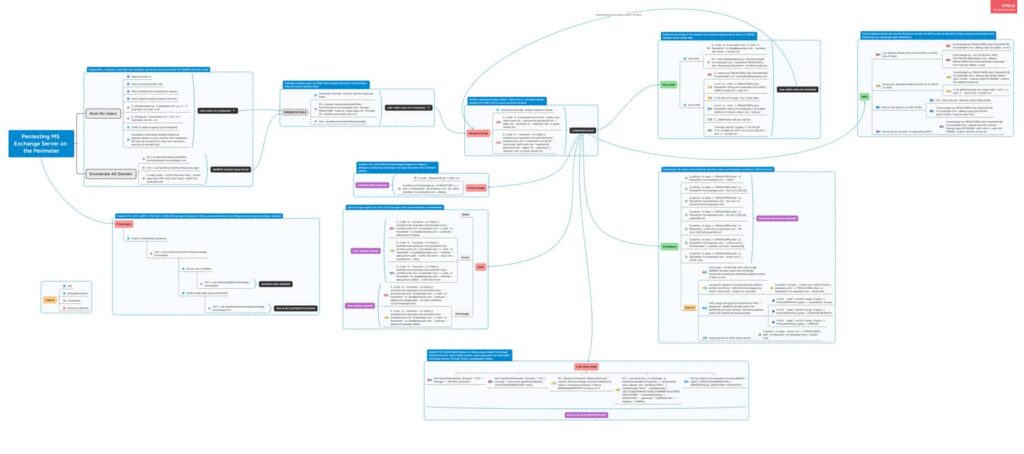
Exchange Mindmap (thx to @snovvcrash)
Active directory ACE mindmap

TODO cheatsheets
reverse shell
- msfvenom
- php
- python
- perl
- powershell
- java
- ruby
whitebox analysis grep regex
- php
- nodejs
- hash
Tools
- enum4linux
- smbmap
- smbget
- rpcclient
- rpcinfo
- nbtscan
- impacket
- impacket
- bloodhound
- rubeus
- powerview
- shadow credentials attack
- samaccountname attack
- mitm6
- responder
- ysoserial
- ysoserial.net
bruteforce & pass cracking
- hydra
- hashcat
- john
- nmap
- eyewitness
- gowitness
- gobuster
- ffuf
- wfuzz
- dig
- dnsrecon
- dnsenum
- sublist3r
- rpcbind
- snmpwalk
- snmp-check
- onesixtyone
- sqlmap
- oscanner
- sqlplus
- tnscmd10g
- mysql
- showmount
- xfreerdp
- rdesktop
- ncrack
- sqsh
- evilwinrm
- redis-cli
- psql
- pgdump
- vncviewer
- xspy
- xwd
- xwininfo
- ldapsearch
- sslscan
- burp
- nikto
- tplmap
- drupwn
- wpscan
- nuclei
arsenal (this link opens in a new window) by Orange-Cyberdefense (this link opens in a new window)
Arsenal is just a quick inventory and launcher for hacking programs

