This is a simple script intended to perform a full recon on an objective with multiple subdomains. It performs multiples steps listed below:
- Tools checker
- Google Dorks (based on deggogle_hunter)
- Subdomain enumeration (passive, resolution, bruteforce and permutations)
- Sub TKO (subjack and nuclei)
- Probing (httpx)
- Websscreenshot (aquatone)
- Template scanner (nuclei)
- Port Scan (naabu)
- Url extraction (waybackurls and gau)
- Pattern Search (gf and gf-patterns)
- Param discovery (paramspider and arjun)
- XSS (Gxss and dalfox)
- Github Check (git-hound)
- Favicon Real IP (fav-up)
- Javascript Checks (JSFScan.sh)
- Directory fuzzing/discovery (dirsearch and ffuf)
- Cors (CORScanner)
- SSL Check (testssl)
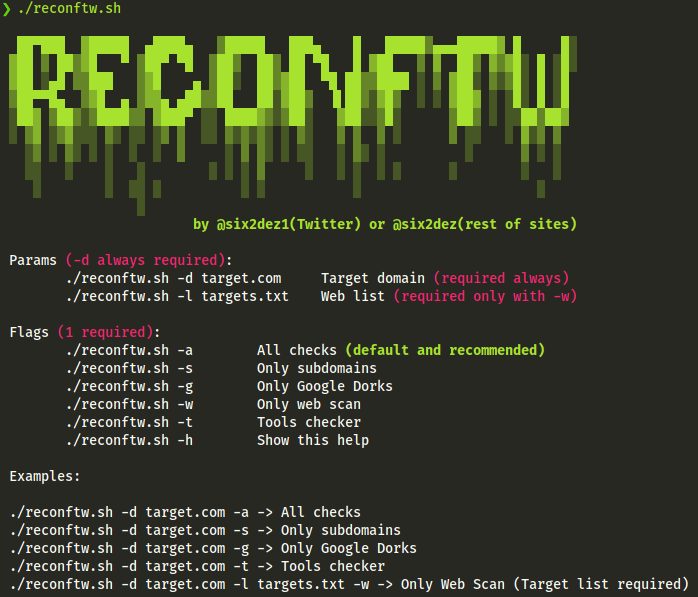
Also you can perform just subdomain scan, webscan or google dorks. Remember webscan needs target lists with -l flag.
It generates and output in Recon/ folder with the name of the target domain, for example Recon/target.com/
Installation
- Requires Go
- install.sh uses apt for installing packages, modify for your needs
git clone https://github.com/six2dez/reconftw
cd reconftw
chmod +x *.sh
./install.sh
./reconftw.sh -d target.com -aUsage
Full scan:
./reconftw.sh -d target.com -a
Subdomains scan:
./reconftw.sh -d target.com -s
Web scan (target list required):
./reconftw.sh -d target.com -l targets.txt -w
Dorks:
./reconftw.sh -d target.com -g
Notes
- Some tools in this script need or can use multiple API keys, such as amass, subfinder, or git-hound. It is up to you to configure them correctly, consult the documentation of each tool to do it correctly.
- This script uses dalfox with blind-xss option, you must change to your own server, check xsshunter.com.
Short-term improvement plan:
- Enhance this Readme
- Customize output folder
- Interlace usage
- Notification support (Slack, Discord and Telegram)
- CMS tools (wpscan, drupwn/droopescan, joomscan)
- Any other interesting suggestion
Dark Mode
reconftw (this link opens in a new window) by six2dez (this link opens in a new window)
Simple script for full recon

