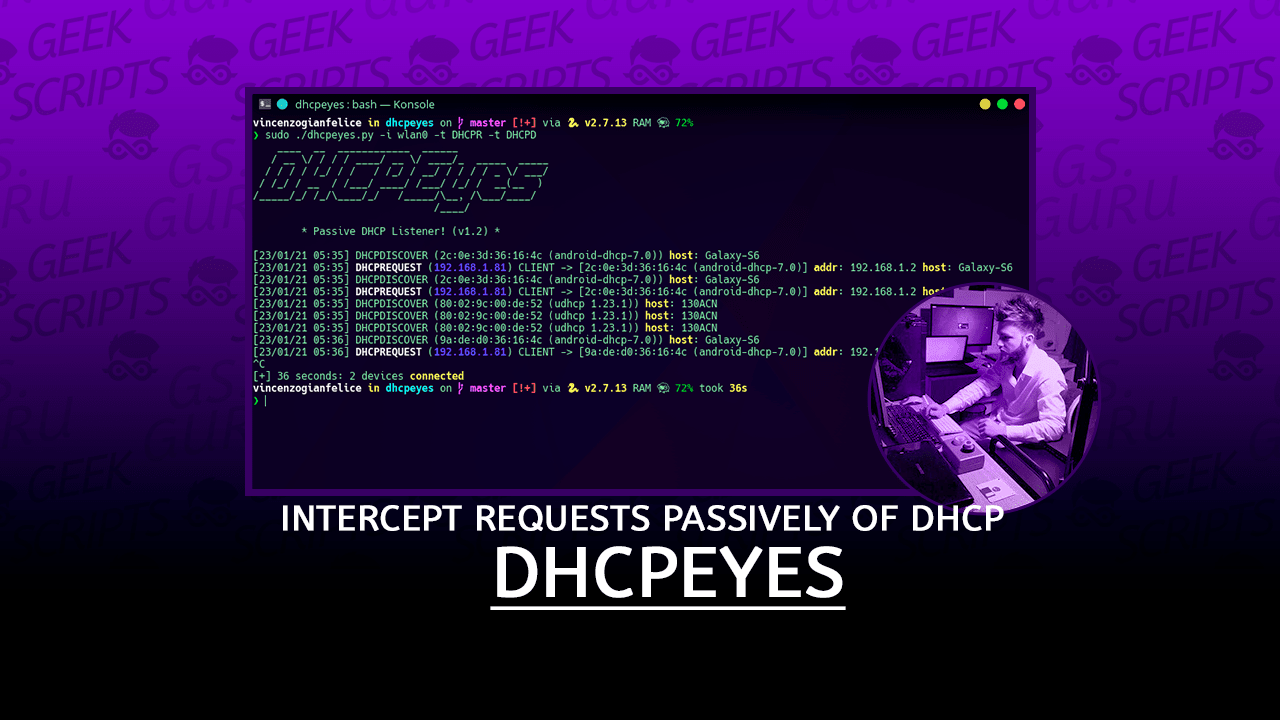
Intercept requests passively of DHCP from own network!

Prerequisites
Require Python2.7 (also Python3.5)
- scapy >= 2.4.4
- termcolor
- colorama (if you use windows)
Windows
- First, install WinPcap
- After installed winpcap, run file exe after downloaded
- For searching interfaces on Windows, digit in prompt
netsh interface show interface, and copy the 4 column (Nome interfaccia/Name interface)
"
"
Installation
pip2 install -r requirements.txt
Usage
____ __ ____________ ______
/ __ \/ / / / ____/ __ \/ ____/_ _____ _____
/ / / / /_/ / / / /_/ / __/ / / / / _ \/ ___/
/ /_/ / __ / /___/ ____/ /___/ /_/ / __(__ )
/_____/_/ /_/\____/_/ /_____/\__, /\___/____/
/____/
* Passive DHCP Listener! (v1.2) *
Usage: ./dhcpeyes.py -i <interface>
-i Interface for listening
Optional:
-o <arg> File Output Save
-t <arg> Options types: DHCPD (discover)
DHCPR (request)
DHCPN (nak)
DHCPI (inform)
Default print all optionsExamples
- Intercept only DHCPREQUEST on wlan0
./dhcpeyes.py -i wlan0 -t DHCPR- Intercept DHCPINFORM and DHCPDISCOVER
./dhcpeyes.py -t DHCPI -i wlan0 -t DHCPD- Intercept all
./dhcpeyes.py -i wlan0 Windows
Using “Connessione alla rete locale (LAN)” provided from output of command netsh
./dhcpeyes.py -i "Connessione alla rete locale (LAN)" -t DHCPR
Dark Mode
DHCPEyes (this link opens in a new window) by vincenzogianfelice (this link opens in a new window)
:eyes: Intercept requests passively of DHCP from own network! :eyes: