Avyukt is a Exploitation Framework which can be used to generate Malicious Payloads and exploit Windows OS. For now, I have only released a Beta Version for now. More updated features and better payloads are going to be added soon in the final version.
General Info about the Framework
Avyukt is a Framework which can generate Malicious Payloads for getting remote access on Windows Computers
The Framework is still under Developement and I am just releasing a Beta Version of it right now
Setting Up Avyukt
To use the Framework, You can simply download it as a ZIP File or you can clone it using this command
git clone https://github.com/Vedant-Bhalgama/Avyukt.git
Before running the setup.py run these 2 commands first or else you will get error
pip install colorama
pip install pyfigletNow, You need to direct to the directory Avyukt_Setup to run the setup.py file.
Simply type this command to run the setup
python ./setup.py

Getting Started with Avyukt
To start the Framework, You need to run this command
python ./Avyukt.py
You will see a menu like this

If you run the Framework for the first time, Directory called Output will be created
- To Generate Malicious Payload, Type 1
- To use Listeners, Type 2
- To use Help, Type 3
- To Exit Framework, Type 4
Evasion
You will get a view like this when you enter the Evasion Menu
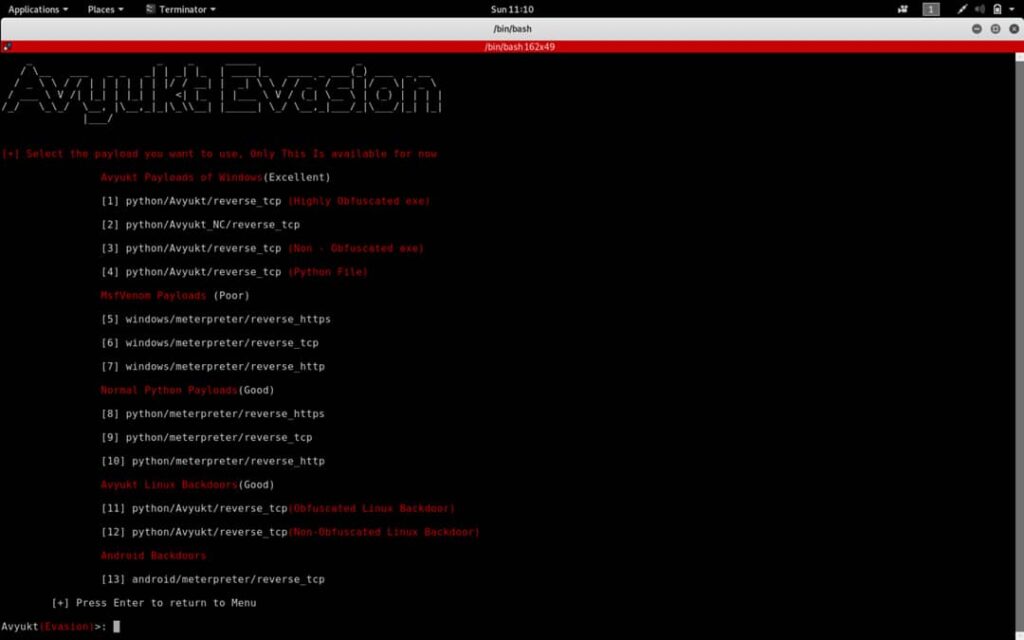
Please remember that the Framework is still under Beta Developement, More Upgrades and Updates are going to come soon
For the best results, Please use 1st payload or In-Built Avyukt Payloads as they are the best in Bypassing Anti-Virus. New implementations are going to be added soon
While generating Paylods, Keep a legit name of the Backdoor which is going to be generated as they also help in Bypassing AV, If you keep a name which looks malicious like test.exe or payload.exe it will be easily detected
For Eg. I was to use the 1st Payload, Simply type 1 or any other number in the menu you wanna use
After you choose the payload you want to use, You will have to enter values for Name, LHOST and LPORT. After you have given values for these parameters, You simply have to choose y or n if you have to add icon to the Executable which will be generated. Please note only .ico files are supported.Now, You have to enter the path to the .ico file and the Framework will do the rest.

Handlers
You will see a view like this after you enter the Handler Menu

What is Avyukt Handler?
- Avyukt Handler is the Default Handler for the In-Built Avyukt Payloads which were Programmed by me
- Payloads like
python/Avyukt/reverse_tcpare compatible with Avyukt Handler
What is NetCat Handler?
- NetCat is a very popular tool which you must be knowing.
- There are some payloads in the Framework which require NetCat as a listener
What is Metasploit?
- Come on man, You must be knowing about Metasploit, I dont have to tell it!
Features of Avyukt Payload
Here are some of the features which are found in the default Avyukt Payloads, Avyukt Payloads are programmed by me in Python.
- Screenshot Ability
- Upload Files
- Download Files
- Webcam Hacking and streaming live (I have not added it in this release as it is not stable, I will add it in the next update)
- Execute any System Command (notepad.exe or any other system command)
- Directory Navigation (cd command)
- Persistent
Avyukt (this link opens in a new window) by Vedant-Bhalgama (this link opens in a new window)
Avyukt is a Exploitation Framework which can be used to generate Malicious Payloads and exploit Windows OS
