Use this tool to make penetration tests or any hacking CTF’s more efficient. This tool should be used on applications that you have permission to attack only. Any misuse or damage caused will be solely the users’ responsibility.
Karkinos is a light-weight ‘Swiss Army Knife’ for penetration testing and/or hacking CTF’s. Currently, Karkinos offers the following:
- Encoding/Decoding characters
- Encrypting/Decrypting text or files
- Reverse shell handling
- Cracking and generating hashes
Dependencies
- Any server capable of hosting PHP
- Tested with PHP 7.4.9
- Tested with Python 3.8
Make sure it is in your path as:
Windows:python
Linux:python3
If it is not, please change the commands inincludes/pid.php - pip3
- Raspberry Pi Zero friendly 🙂 (crack hashes at your own risk)
Installing
This installation guide assumes you have all the dependencies. A Wiki page for installation, troubleshooting, and usage is coming very soon…
Linux/BSD
git clone https://github.com/helich0pper/Karkinos.git
cd Karkinos
pip3 install -r requirements.txt
cd wordlists && unzip passlist.zipYou can also unzip it manually using file explorer. Just make sure passlist.txt is in wordlists directory.
- Enable
extension=mysqliin your php.ini file.
If you don’t know where to find this, refer to the PHP docs. Note: MySQLi is only used to store statistics.
Thats it! Now just host it using your preferred web server or run: php -S 127.0.0.1:8888 in the Karkinos directory.
Important: using port 5555, 5556, or 5557 will conflict with the Modules
If you insist on using these ports, change the PORT value in:
/bin/Server/app.py Line 87
/bin/Busting/app.py Line 155
/bin/PortScan/app.py Line 128Windows
git clone https://github.com/helich0pper/Karkinos.git
cd Karkinos
pip3 install -r requirements.txt
cd wordlists && unzip passlist.zipYou can also unzip it manually using file explorer. Just make sure passlist.txt is in wordlists directory.
- Enable
extension=mysqli.dllin your php.ini file.
If you don’t know where to find this, refer to the PHP docs. Note: MySQLi is only used to store statistics
Thats it! Now just host it using your preferred web server or run: php -S 127.0.0.1:8888 in the Karkinos directory.
Important: using port 5555, 5556, or 5557 will conflict with the Modules
If you insist on using these ports, change the PORT value in:
/bin/Server/app.py Line 87
/bin/Busting/app.py Line 155
/bin/PortScan/app.py Line 128Demo
Open screenshots in full screen for a better view
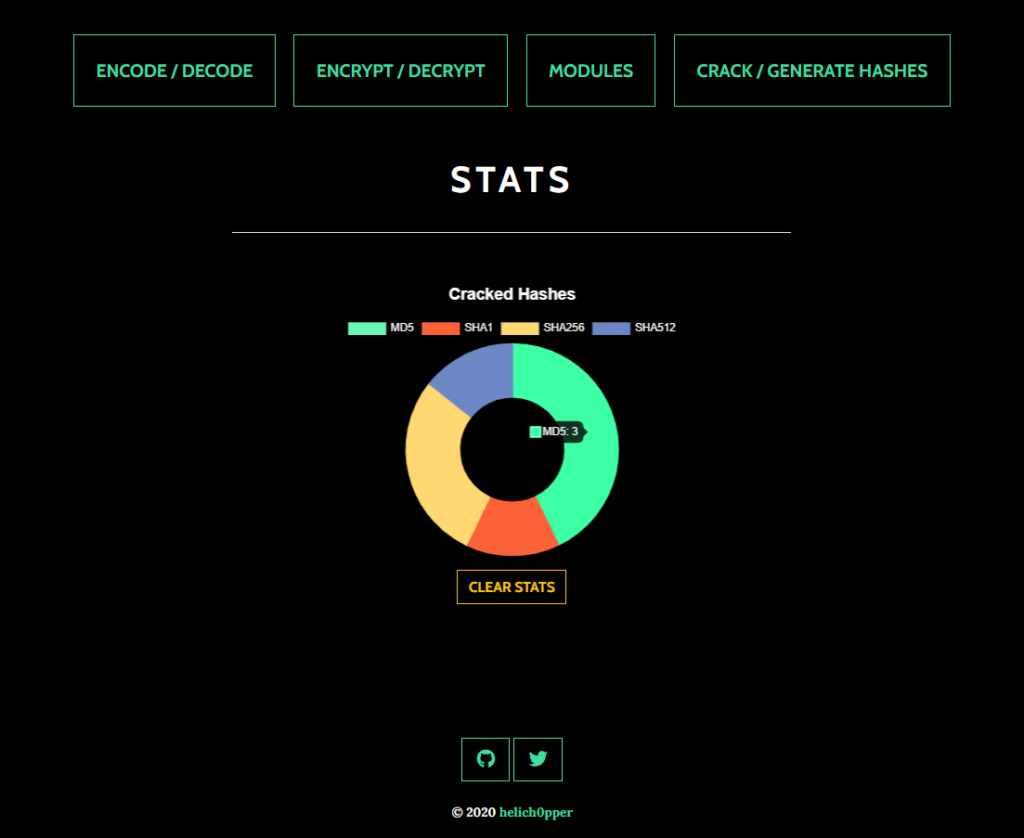
Home Menu
Landing page and quick access menu.

User stats are displayed here. Currently, the stats recorded are only the total hashes and hash types cracked successfully.
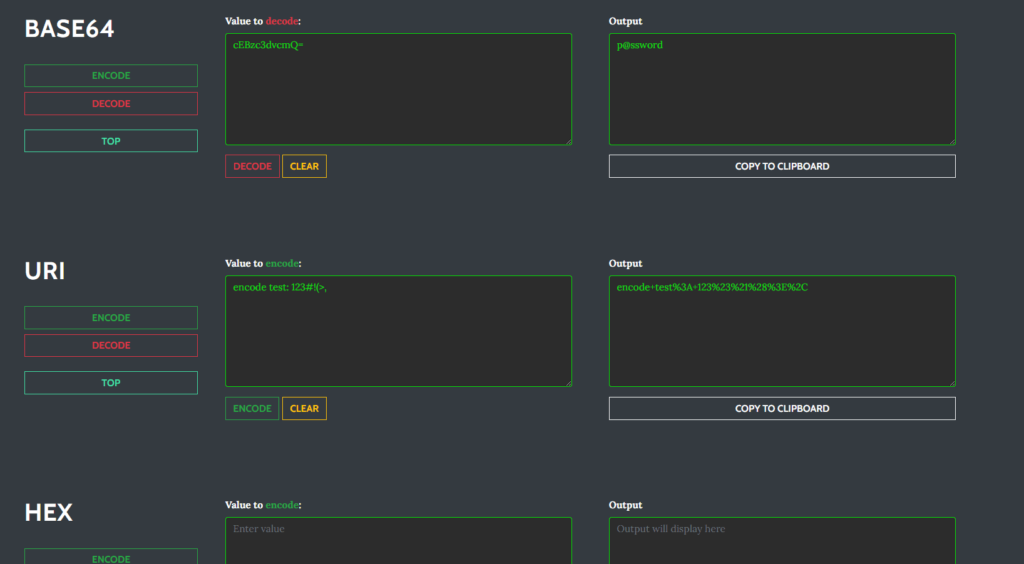
Encoding/Decoding
This page allows you to encode/decode in common formats (more may be added soon)
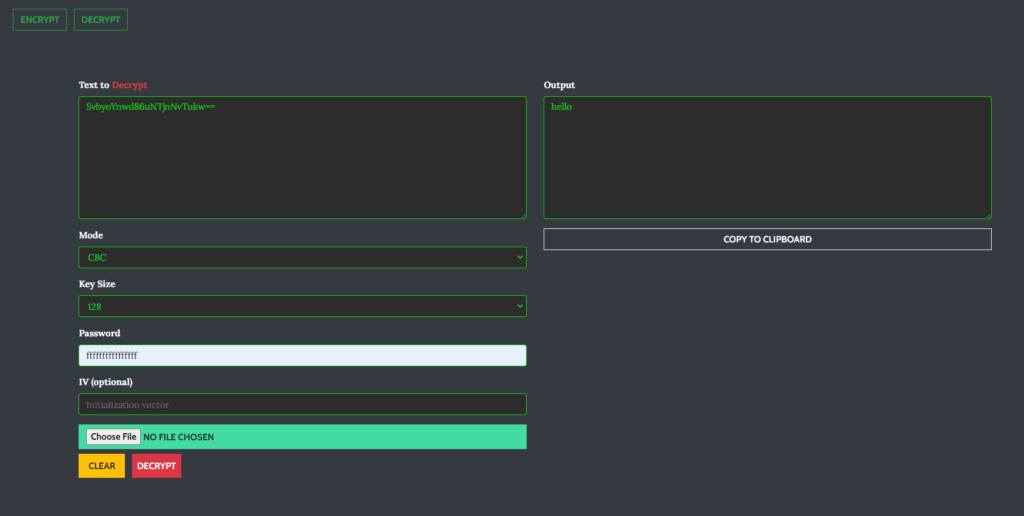
Encrypt/Decrypt
Encrypting and decrypting text or files is made easy and is fully trusted since it is done locally.
Modules
More modules will be added.
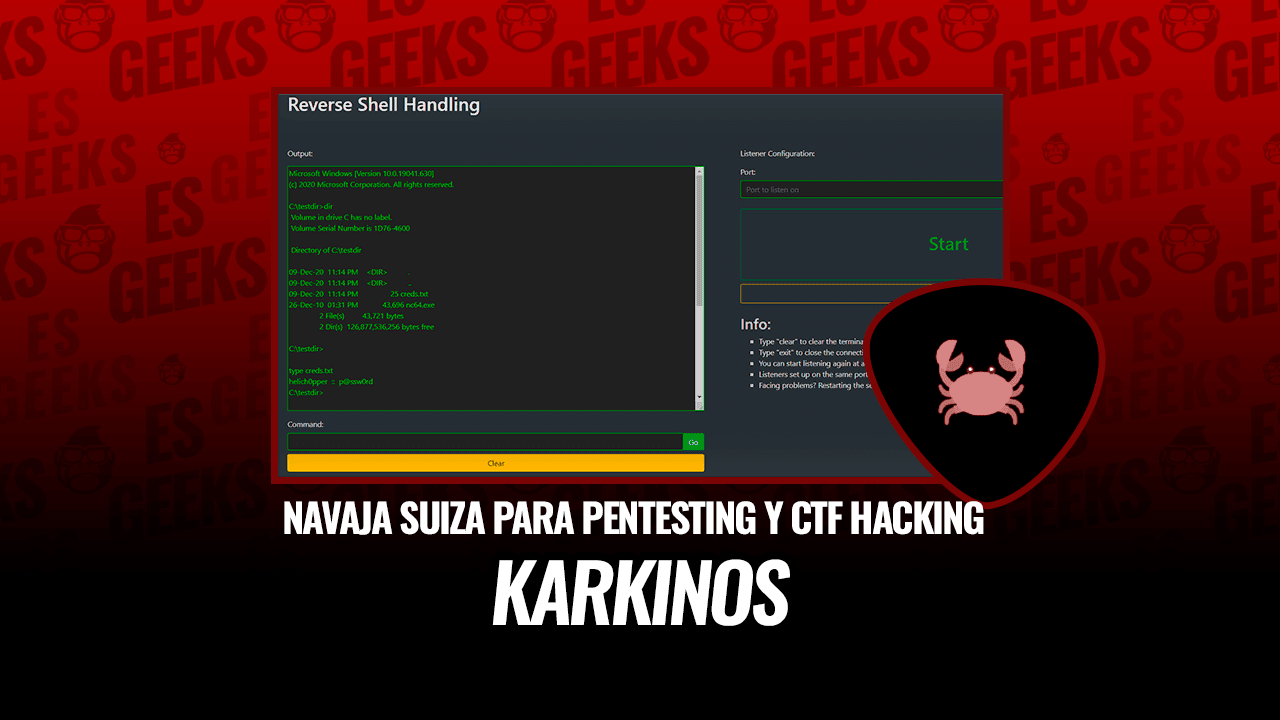
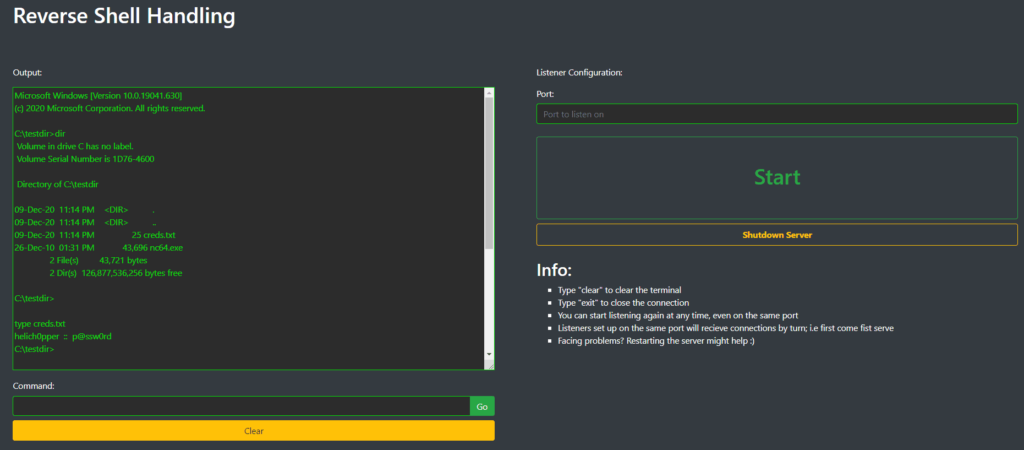
Reverse Shell Handling
Reverse shells can be captured and interacted with on this page.

Configure the listener
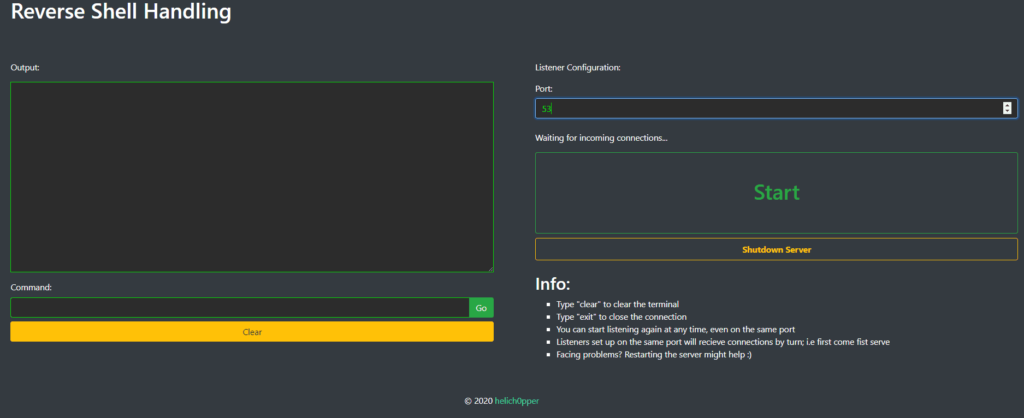
Start the listener and capture a shell
Directory and File Busting
Create an instance

Configure it

Start scanning

Port Scanning
Launch the scanner

Configure it

Start scanning

Generating Hashes
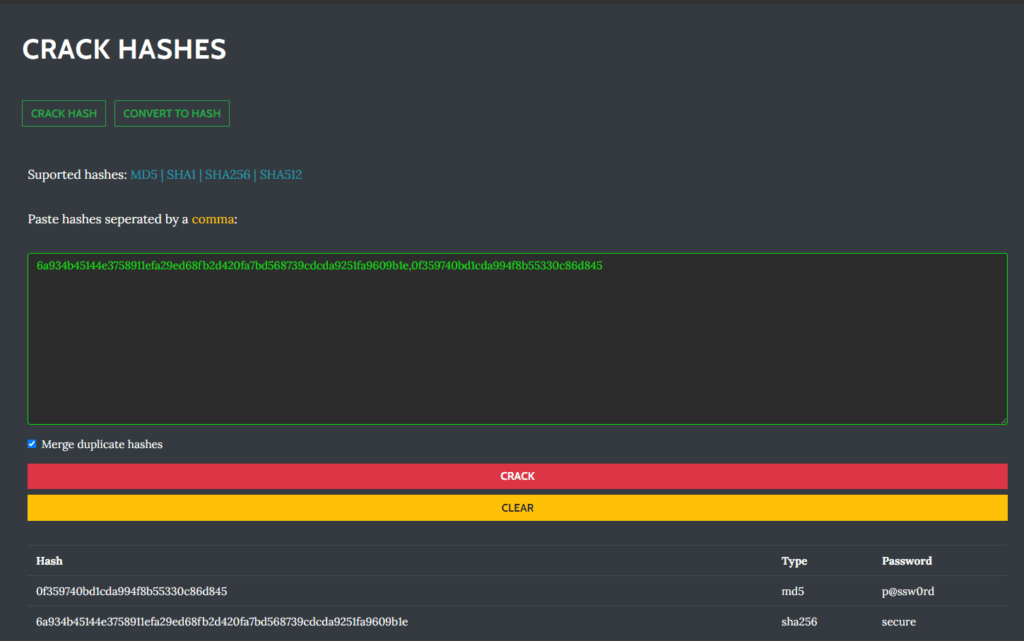
Karkinos can generate commonly used hashes such as:
- MD5
- SHA1
- SHA256
- SHA512

Cracking Hashes
Karkinos offers the option to simultaneously crack hashes using a built-in wordlist consisting of over 15 million common and breached passwords. This list can easily be modified and/or completely replaced.
Karkinos (this link opens in a new window) by helich0pper (this link opens in a new window)
Penetration Testing and Hacking CTF’s Swiss Army Knife with: Reverse Shell Handling – Encoding/Decoding – Encryption/Decryption – Cracking Hashes / Hashing